Compare Protocols, Optimize Deployment
VPN establish encrypted tunnels over public networks to protect industrial IIoT data from interception and tampering, as unencrypted transmissions expose critical infrastructure to cyber threats and data transmission vulnerabilities account for a large share of global industrial network attacks. With OpenVPN and IPsec serving as the dominant VPN protocols for industrial IoT deployments—each offering unique advantages in security, performance, and deployment flexibility. Bivocom evaluates both across technical architecture, performance, complexity, and real-world use cases to help engineers select the optimal VPN security solution for their IIoT applications.
What is VPN, and Why It Matters for IoT
VPN (Virtual Private Network) creates a secure, private communication channel over a public network. It encrypts data at the sending endpoint, transmits it through a tunnel, and decrypts it at the receiving endpoint. In simple terms, think of it as sending a sealed, armored box through a public courier service — instead of mailing a postcard that anyone can read along the way, you place your message inside a locked box. Only the sender and receiver have the key, so even if the box is intercepted, the contents remain unreadable and unaltered. This process ensures three critical protections: confidentiality (only authorized parties can read the data), integrity (data cannot be altered undetected during transit), and authentication (endpoints verify each other’s identity before any exchange).
For IoT deployments, VPNs address three fundamental challenges:
- Data security: Encryption renders industrial commands, sensor readings, and process parameters unreadable to attackers.
- Cross‑domain networking: VPNs support dynamic IP addressing and multi‑protocol encapsulation, enabling flexible connectivity across geographic regions and mobile carriers without costly dedicated lines.
- Remote operations: Engineers can securely access field devices for parameter adjustments, firmware updates, and troubleshooting without traveling to the site.
VPN types and protocols – VPNs generally fall into two deployment models: site‑to‑site (connecting entire networks) and remote access (connecting individual devices or users). A range of protocols support these models, including OpenVPN, IPsec, WireGuard, L2TP/IPsec, and IKEv2. Among them, OpenVPN and IPsec are the most widely deployed in industrial IoT environments. OpenVPN, built on SSL/TLS, is valued for its ease of firewall traversal and simple configuration. IPsec, a standardized IETF suite, offers kernel‑level performance and native OS support. Together, they provide the most practical balance of security, performance, and deployment flexibility for IIoT applications.
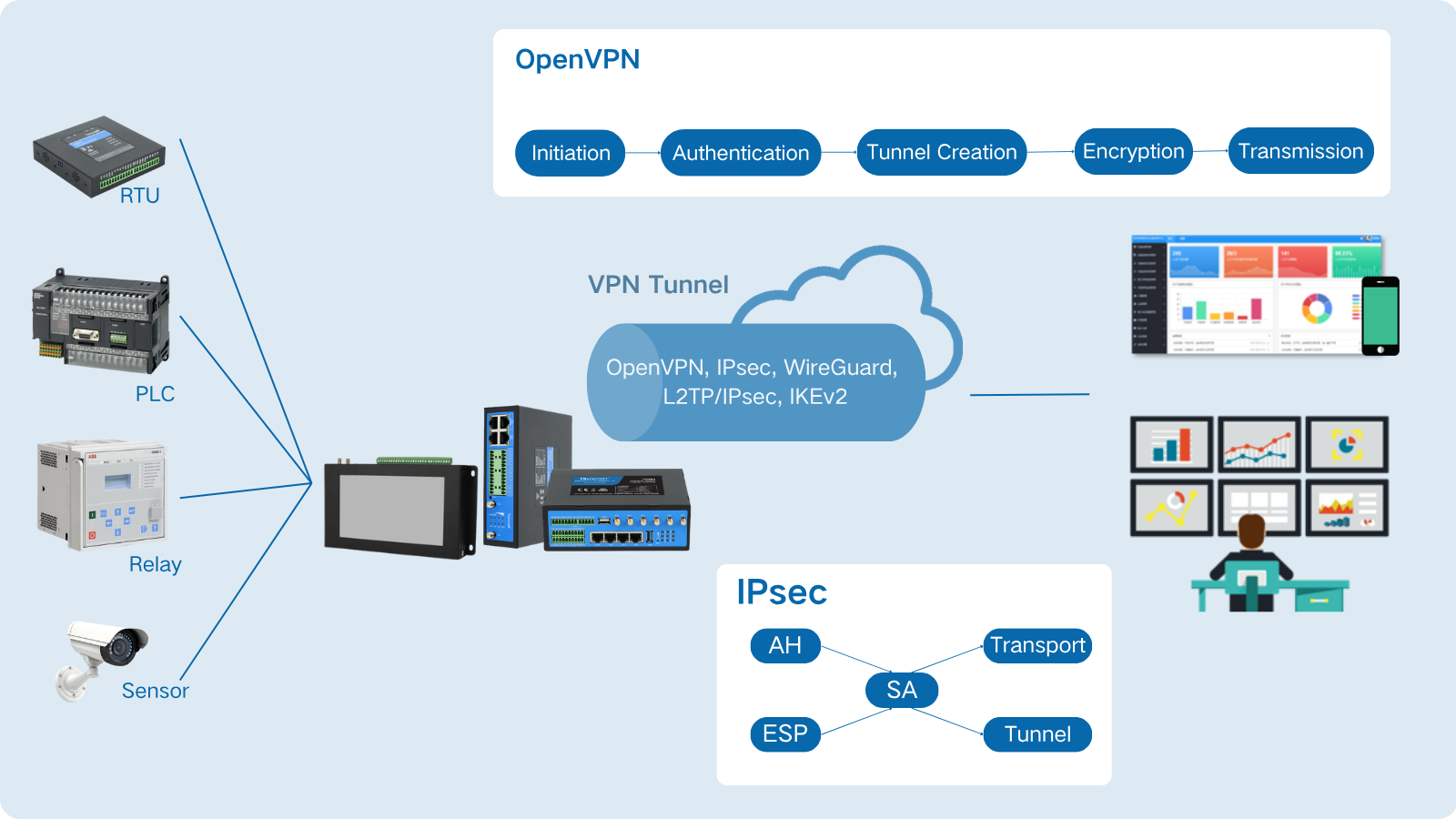
OpenVPN
OpenVPN is an open-source VPN solution that builds secure, encrypted tunnels over public networks. Unlike IPsec, which operates inside the operating system kernel, OpenVPN runs at the application layer. This design gives it remarkable flexibility. It uses the SSL/TLS protocol for authentication and key exchange, paired with strong encryption algorithms to protect data. OpenVPN supports multiple authentication methods — certificates, pre-shared keys, or usernames and passwords — making it adaptable to various security requirements.
How OpenVPN Works
OpenVPN creates a virtual network interface (TUN for IP routing or TAP for Ethernet bridging) on the device. When an application sends data, the operating system directs that data to this virtual interface instead of the physical network. OpenVPN’s software then encrypts each packet, wraps it inside a new UDP or TCP packet, and sends it to the VPN server. The server reverses the process: decrypts the packet, verifies its integrity, and forwards it to the final destination. All communication happens over a single port, which simplifies firewall configuration.
Key Strengths
- Firewall traversal: Runs on TCP port 443, mimicking HTTPS traffic. This lets IoT devices connect from behind restrictive corporate firewalls and cellular carrier NAT.
- Simple deployment: All certificates, keys, and settings bundle into one configuration file. Pre-load it during manufacturing; devices connect automatically on first boot.
- Performance acceleration (DCO): The DCO kernel module moves encryption into the kernel, boosting throughput 3–10× on compatible hardware and closing the performance gap with IPsec.
IPsec
IPsec (Internet Protocol Security) is an IETF‑standardized suite that secures IP communications directly inside the operating system kernel. Unlike OpenVPN (user space), this kernel‑level design delivers high throughput with low CPU overhead. IPsec provides encryption, authentication, and integrity for every IP packet through three core components: ESP (encryption + integrity), AH (integrity only), and IKE (key exchange and Security Association setup).
How IPsec Works
IPsec has two modes. Transport mode encrypts only the packet payload — suitable for host‑to‑host communication. Tunnel mode encrypts the entire IP packet and wraps it in a new IP header, forming the basis of network‑to‑network VPNs. The process starts with IKEv2 authenticating both peers (using certificates or pre‑shared keys) and negotiating encryption algorithms. Once they agree, a Security Association (SA) defines how to protect the traffic. All subsequent packets go through kernel‑level ESP processing — encryption, hashing, and encapsulation never leave kernel space. On Linux, the XFRM framework enforces these policies. If a device roams between networks, the MOBIKE extension keeps the VPN session alive seamlessly.
Key Strengths
- Kernel-level performance: Processes packets directly in the kernel, delivering higher throughput and lower CPU load than legacy OpenVPN.
- Native OS support: Built into Windows, macOS, iOS, Android, and Linux. No extra client software required.
- MOBIKE for mobility: Seamless roaming across Wi‑Fi, cellular, or cell towers — essential for vehicles, drones, and mobile IoT.
- Hardware acceleration: Many industrial processors include dedicated IPsec crypto engines, enabling line‑rate VPN on resource‑constrained gateways.
- Standards compliance: IETF standard required for government, defense, and regulated industries; decades of security analysis.
OpenVPN vs. IPsec
To simplify your protocol selection for industrial IoT deployments, we’ve compiled a direct, engineering-focused comparison of core performance, deployment, and operational traits below.
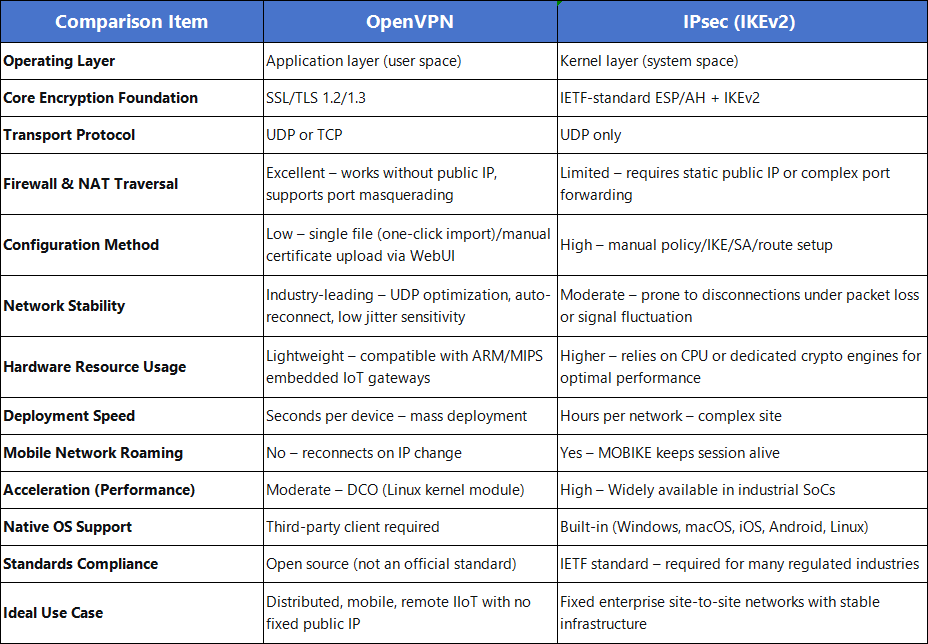
Notes: OpenVPN: simple client mode via one‑click .ovpn file or full server/client setup with certificate/DH upload. IPsec: manual policy setup (IKE/SA/route rules).
About Bivocom
Industrial IoT deployments no longer need to struggle with fragile VPN connections, complex manual configurations, or protocol mismatches. The choice between OpenVPN and IPsec depends on your network environment, device resources, and operational needs. Bivocom rugged hardware (GNSS/LoRa/5G routers, gateways, and RTUs) support both protocols, so you can keep your industrial data safe without sacrificing reliability or performance. We turn challenging network environments into reliable, manageable assets.
- Customized Protocol Consulting: Expert guidance to match OpenVPN or IPsec with your network and device constraints.
- Simplified Deployment Support: Pre‑loaded configs and auto‑connect for hassle‑free mass deployment.
- Long‑Term Operational Support: Ongoing firmware updates and remote troubleshooting to keep VPN tunnels secure and stable.
Ready to Elevate Your IIoT Network Security?
Take the first step toward reliable, future‑proof industrial connectivity. Reach out to Bivocom today at [email protected] — we’re here to help you unlock the full potential of your VPN deployment.



Comment